Sometimes, you just have to look into the raw data to see what your web server is doing. The logs might not show you enough detail or you suspect something is going on which is just not shown in the log files. Or, as in my case, logging is turned off because of too much activity.
The excellent tcpdump utiliy comes to the rescue here. I recommend you get more familiar with the tcpdump man page. Here is the command you can use, in a nutshell:
tcpdump -nl -w - -i eth1 -c 500 port 80|strings
or alternatively with just tcpdump (Thanks Chris!):
tcpdump -nl -s 0 -A -i eth1 -c 500 port 80
Your command line will print out all traffic exiting your server from port 80, headers and all. Lets look at the options in more detail.
- -n: Don’t convert addresses (i.e., host addresses, port numbers, etc.) to names.
- -l: Make stdout line buffered. Useful if you want to see the data while capturing it.
- -w: Write the raw packets to file rather than parsing and printing them out. (Sent to stdout)
- -i: Interface you want to sniff on, usually eth0 or eth1, but depends on your system.
- -c: Number of packets to capture
- port: port 80, duh :)
- -A: Print each packet (minus its link level header) in ASCII.
- -s: size
Now, depending on your web server configuration, you will probably have gzipped content which comes out as garbled characters. To strip all that out, just pipe it through strings.
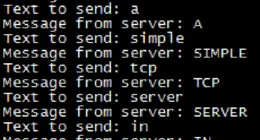
The output will look something like this:
GET /about/comment-page-1 HTTP/1.0
Accept: image/gif, image/jpeg, image/pjpeg, application/x-ms-application, application/vnd.ms-xpsdocument, application/xaml+xml, application/x-ms-xbap, application/vnd.ms-excel, application/vnd.ms-powerpoint, application/msword, application/x-shockwave-flash, */*
User-Agent: Mozilla/2.0 (compatible; MSIE 3.02; Windows CE; 240x320)
Referer: http://quittingsoda.com/about/comment-page-1#comment-6637
Host: quittingsoda.com
Cookie: comment_author_xxx=sakyjartory; comment_author_email_26e707905b5fd6e7139333eb1dab208f=olfaexxxx; comment_author_url_26e707905b5fd6e7139333eb1dab208xxx
HTTP/1.1 200 OK
Date: Wed, 03 Oct 2012 01:49:19 GMT
Server: Apache/2
X-Powered-By: PHP/5.2.17
X-Pingback: http://quittingsoda.com/xmlrpc.php
Vary: Accept-Encoding,User-Agent
Connection: close
Content-Type: text/html; charset=UTF-8
Let me know if you have any suggestions for improving this simple command line program for sniffing your web server traffic! Netcat is an essential tool that every linux administrator should get to know better.



1 comment
Instead if using `tcpdump -w – | strings` why not do something like `tcpdump -s 0 -A`. or use `-X` if you want the hexidecimal output.
-A Print each packet (minus its link level header) in ASCII.
-s size
Comments are closed.